How to Complete Cybersecurity Questionnaires: A Practical Outline for IT and Security Teams
Introduction
IT security questionnaire help, CMMC questionnaire answers, NIST 800-171 questionnaire support, federal contractor compliance questionnaire, DFARS compliance questionnaire, cybersecurity questionnaire assistance, CUI compliance questions, how to answer security questionnaires, CMMC readiness questionnaire, IT compliance documentation support
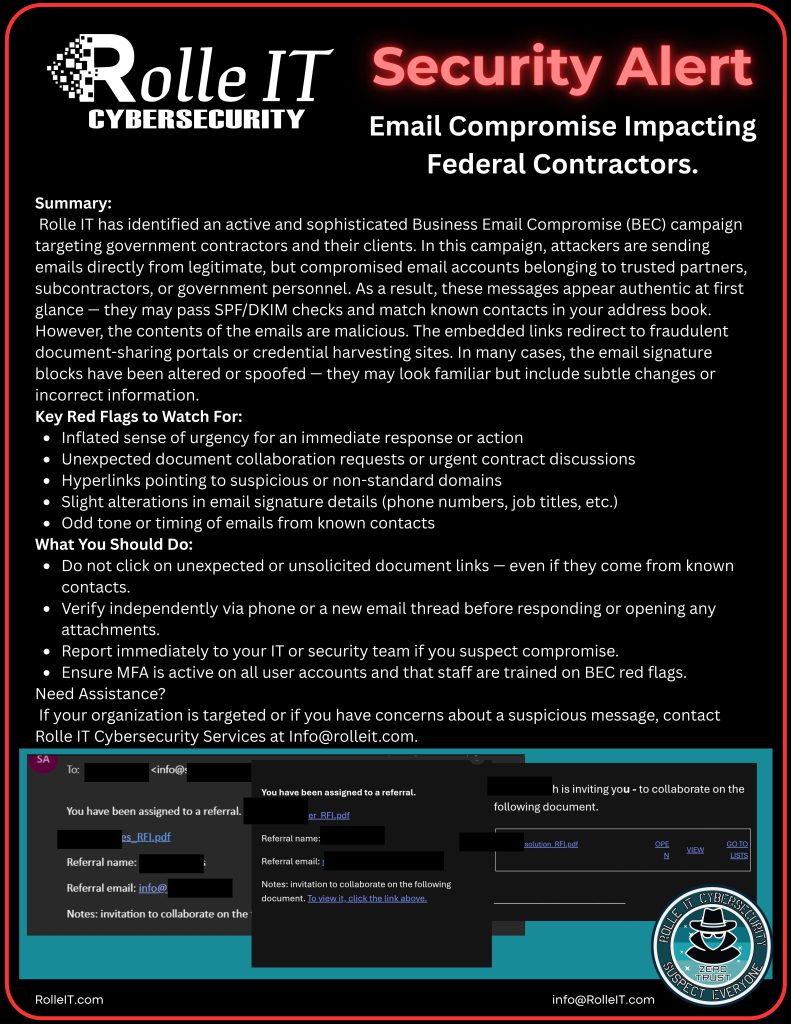
These questionnaires—issued by customers, insurers, partners, auditors, or regulatory bodies—are not simple checklists. They are designed to validate whether your organization can effectively manage cybersecurity risk and protect sensitive data.
Depending on the context, they may align to frameworks such as:
- NIST SP 800-171
- NIST Cybersecurity Framework (CSF)
- CIS Critical Security Controls
- ISO 27001
- CMMC (for DoD-related work)
- Custom requirements
This article outlines how to approach these questionnaires effectively, avoid common pitfalls, and position your organization as audit-ready.
Why IT Security Questionnaires Matter
IT security questionnaires are not limited to DoD or CMMC-driven contracts. Organizations encounter them across multiple contexts, including:
- Cybersecurity insurance applications and renewals
- State, Local, and Education (SLED) contracts
- Vendor risk assessments from partners and primes
- General third-party risk management programs
Each of these questionnaires may vary in complexity, but they all serve a similar purpose: evaluating your organization’s ability to manage cybersecurity risk and protect sensitive data.
Security maturity expectations are increasing across all sectors—not just federal contracting. As a result, even “simpler” questionnaires often include controls aligned to frameworks like NIST 800-171, NIST CSF, or CIS Controls.
Security questionnaires are often the first gate to winning or maintaining contracts.
They are used to:
- Validate your cybersecurity posture before award
- Assess risk in the supply chain
- Determine eligibility for handling CUI
- Pre-screen organizations for CMMC readiness
Poor or inconsistent responses can:
- Delay contract awards
- Trigger additional scrutiny
- Disqualify your organization
What These Questionnaires Are Really Testing
Most questionnaires map directly to NIST SP 800-171 control families.
They are not just asking what tools you use—they are evaluating whether you can:
- Demonstrate control implementation
- Provide supporting evidence
- Align technical controls with documented policies
- Show repeatable, enforceable processes
In other words, they are testing program maturity, not just technology.
Common Challenges IT Teams Face
1. Interpreting the Questions Correctly
Many questions are written in compliance language, not operational language. For example:
“Does your organization enforce least privilege across all systems?”
This requires both:
- Technical enforcement (RBAC, PIM, etc.)
- Documented policy and governance
2. Inconsistent or Unsupported Answers
A common issue is answering “Yes” without:
- Documented procedures
- Configurations to support the claim
- Evidence (logs, screenshots, reports)
This creates risk during audits or follow-up reviews.
3. Lack of Alignment Between IT and Leadership
Security questionnaires often require input beyond IT:
- Legal (contracts, data handling)
- HR (personnel security)
- Executive leadership (risk acceptance)
Without coordination, responses can be incomplete or contradictory.
4. Time Constraints and Resource Limitations
Completing questionnaires thoroughly can take:
- Dozens of hours
- Cross-functional coordination
- Technical validation and documentation
For lean IT teams, this becomes a major operational burden.
A Structured Approach to Completing Questionnaires
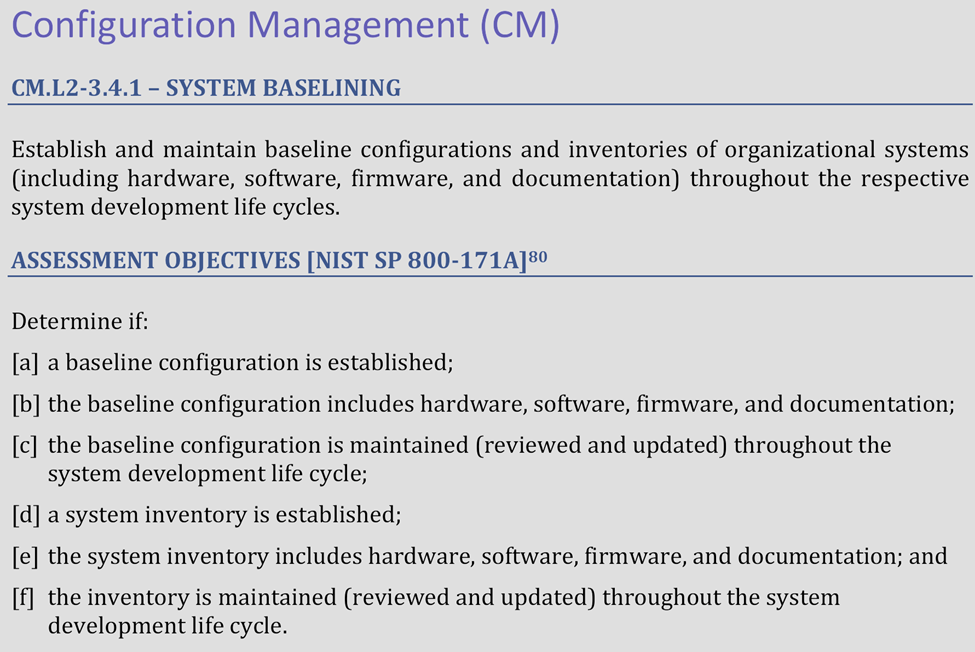
1. Map Questions to NIST 800-171 Controls
Instead of answering each question independently, map them to:
- Control families (AC, AU, IA, SI, etc.)
- Specific control IDs (e.g., AC.2.001)
This ensures consistency across responses.
2. Build a Centralized Evidence Repository
Maintain documentation such as:
- System Security Plan (SSP)
- Policies and procedures
- Configuration baselines
- Audit logs and reports
This allows you to reuse validated responses.
3. Standardize Response Language
Develop pre-approved response statements for common controls.
Example structure:
- Control intent
- How it is implemented
- Tools used
- Reference to policy/evidence
This improves accuracy and reduces rework.
4. Involve the Attesting Official and Leadership
Security questionnaires often imply attestation of compliance.
This means:
- Responses should reflect organizational risk decisions
- Leadership must understand what is being claimed
- The Attesting Official may ultimately be accountable
Cybersecurity is not just an IT responsibility. It is a company-wide program.
5. Validate Before Submission
Before submitting:
- Review for consistency across answers
- Ensure claims match actual configurations
- Confirm documentation exists for each “Yes”
Treat the questionnaire like a pre-audit.
How Microsoft Environments Can Support Responses
Organizations using Microsoft 365 (GCC or GCC High) can leverage native tools to support questionnaire responses:
- Entra ID → Access control, MFA, identity governance
- Defender Suite → Endpoint, identity, and email protection
- Purview → Data classification, DLP, compliance controls
- Microsoft Sentinel → Logging, monitoring, SIEM
When properly configured, these tools provide both:
- Control implementation
- Evidence for validation
Common Mistakes That Lead to Failed Reviews
- Treating questionnaires as administrative tasks
- Overstating capabilities (“Yes” without evidence)
- Ignoring documentation requirements
- Lack of executive awareness or approval
When to Bring in Expert Support
Organizations often seek assistance when:
- Questionnaires become more technical or detailed
- Contracts require higher levels of assurance
- Internal teams lack compliance experience
- There is concern about audit readiness
Expert support can help:
- Translate compliance requirements into accurate responses
- Validate technical controls
- Ensure alignment with CMMC expectations
Conclusion
IT security questionnaires are not just paperwork, they are a critical component of demonstrating compliance and securing federal contracts.
A structured, evidence-based approach, combined with leadership involvement, ensures your responses accurately reflect your organization’s capabilities and readiness.
Organizations that treat questionnaires as part of a broader compliance program are far more likely to succeed in compliance needs.
About Rolle IT Cybersecurity
Rolle IT Cybersecurity is a Managed Security Service Provider (MSSP) specializing in supporting the Defense Industrial Base and federal contractors.
We help organizations:
- Complete complex IT security questionnaires
- Align responses with NIST 800-53 NIST 800-171, CMMC and other targeted frameworks
- Validate technical controls and documentation
- Prepare for audits and contract requirements
If your team is struggling with compliance questionnaires or needs validation before submission, Rolle IT can provide expert support. [email protected]